Configure LDAP Server2011/03/09 |
| Build LDAP Server in order to share users' accounts among local networks. |
|
| [1] | Install openldap |
|
root@master:~# aptitude -y install slapd ldap-utils # Input LDAP admin password during installation 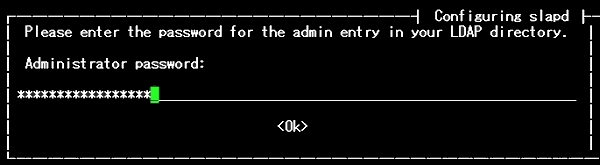 # check working root@master:~# ldapsearch -LLL -Y EXTERNAL -H ldapi:/// -b cn=config dn SASL/EXTERNAL authentication started SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth SASL SSF: 0 dn: cn=config dn: cn=module{0},cn=config dn: cn=schema,cn=config dn: cn={0}core,cn=schema,cn=config dn: cn={1}cosine,cn=schema,cn=config dn: cn={2}nis,cn=schema,cn=config dn: cn={3}inetorgperson,cn=schema,cn=config dn: olcBackend={0}hdb,cn=config dn: olcDatabase={-1}frontend,cn=config dn: olcDatabase={0}config,cn=config dn: olcDatabase={1}hdb,cn=config |
| [2] | Edit existing directories |
|
root@master:~# slappasswd # generate password New password: # input Re-enter new password: {SSHA}XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX # set admin password to config directory root@master:~# ldapmodify -Y EXTERNAL -H ldapi:/// SASL/EXTERNAL authentication started SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth SASL SSF: 0 # input follows ( set password generated above for 'olcRootPW' )
dn: olcDatabase={0}config,cn=config add: olcRootPW olcRootPW: {SSHA}XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX # push 'Ctrl+D' to quit root@master:~# vi config.ldif # create new # change to your own suffix for the field 'dc=server,dc=world'
dn: olcDatabase={1}hdb,cn=config changetype: modify replace: olcSuffix olcSuffix: dc=server,dc=world - replace: olcRootDN olcRootDN: cn=admin,dc=server,dc=world - replace: olcAccess olcAccess: to attrs=userPassword by dn="cn=admin,dc=server,dc=world" write by anonymous auth by self write by * none olcAccess: to attrs=shadowLastChange by self write by * read olcAccess: to dn.base="" by * read olcAccess: to * by dn="cn=admin,dc=server,dc=world" write by * read - # edit 'olcDatabase={1}hdb' root@master:~# ldapmodify -Y EXTERNAL -H ldapi:/// -f config.ldif SASL/EXTERNAL authentication started SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth SASL SSF: 0 modifying entry "olcDatabase={1}hdb,cn=config" # check working root@master:~# ldapsearch -xLLL -b cn=config -D cn=admin,cn=config -W olcDatabase={1}hdb Enter LDAP Password: # password set above dn: olcDatabase={1}hdb,cn=config objectClass: olcDatabaseConfig objectClass: olcHdbConfig olcDatabase: {1}hdb olcDbDirectory: /var/lib/ldap olcLastMod: TRUE olcRootPW: {SSHA}XXXXXXXXXXZZZZZZZZZZZZZZZ olcDbCheckpoint: 512 30 olcDbConfig: {0}set_cachesize 0 2097152 0 olcDbConfig: {1}set_lk_max_objects 1500 olcDbConfig: {2}set_lk_max_locks 1500 olcDbConfig: {3}set_lk_max_lockers 1500 olcDbIndex: objectClass eq olcSuffix: dc=server,dc=world olcRootDN: cn=admin,dc=server,dc=world olcAccess: {0}to attrs=userPassword by dn="cn=admin,dc=server,dc=world" write by anonymous auth by self write by * none olcAccess: {1}to attrs=shadowLastChange by self write by * read olcAccess: {2}to dn.base="" by * read olcAccess: {3}to * by dn="cn=admin,dc=server,dc=world" write by * read |
| [3] | Add new directory |
|
root@master:~# vi base.ldif # create new # change to your own suffix for the field 'dc=server,dc=world'
dn: dc=server,dc=world objectClass: top objectClass: dcObject objectclass: organization o: Server World dc: Server description: LDAP Server dn: ou=people,dc=server,dc=world objectClass: organizationalUnit ou: people dn: ou=groups,dc=server,dc=world objectClass: organizationalUnit ou: groups root@master:~# ldapadd -x -D cn=admin,dc=server,dc=world -W -f base.ldif Enter LDAP Password: # LDAP admin password (set in installation of openldap) adding new entry "dc=server,dc=world" adding new entry "ou=people,dc=server,dc=world" adding new entry "ou=groups,dc=server,dc=world" |
| [4] | Add existing local users to LDAP directory |
|
root@master:~# vi ldapuser.sh # extract local users who have 4-digit UID # an example
#!/bin/bash SUFFIX='dc=server,dc=world' LDIF='ldapuser.ldif' echo -n > $LDIF for line in `grep "x:[1-9][0-9][0-9][0-9]:" /etc/passwd | sed -e "s/ /%/g"` do UID1=`echo $line | cut -d: -f1` NAME=`echo $line | cut -d: -f5 | cut -d, -f1` if [ ! "$NAME" ] then NAME=$UID1 else NAME=`echo $NAME | sed -e "s/%/ /g"` fi SN=`echo $NAME | awk '{print $2}'` if [ ! "$SN" ] then SN=$NAME fi GIVEN=`echo $NAME | awk '{print $1}'` UID2=`echo $line | cut -d: -f3` GID=`echo $line | cut -d: -f4` PASS=`grep $UID1: /etc/shadow | cut -d: -f2` SHELL=`echo $line | cut -d: -f7` HOME=`echo $line | cut -d: -f6` EXPIRE=`passwd -S $UID1 | awk '{print $7}'` FLAG=`grep $UID1: /etc/shadow | cut -d: -f9` if [ ! "$FLAG" ] then FLAG="0" fi WARN=`passwd -S $UID1 | awk '{print $6}'` MIN=`passwd -S $UID1 | awk '{print $4}'` MAX=`passwd -S $UID1 | awk '{print $5}'` LAST=`grep $UID1: /etc/shadow | cut -d: -f3` echo "dn: uid=$UID1,ou=people,$SUFFIX" >> $LDIF echo "objectClass: inetOrgPerson" >> $LDIF echo "objectClass: posixAccount" >> $LDIF echo "objectClass: shadowAccount" >> $LDIF echo "uid: $UID1" >> $LDIF echo "sn: $SN" >> $LDIF echo "givenName: $GIVEN" >> $LDIF echo "cn: $NAME" >> $LDIF echo "displayName: $NAME" >> $LDIF echo "uidNumber: $UID2" >> $LDIF echo "gidNumber: $GID" >> $LDIF echo "userPassword: {crypt}$PASS" >> $LDIF echo "gecos: $NAME" >> $LDIF echo "loginShell: $SHELL" >> $LDIF echo "homeDirectory: $HOME" >> $LDIF echo "shadowExpire: $EXPIRE" >> $LDIF echo "shadowFlag: $FLAG" >> $LDIF echo "shadowWarning: $WARN" >> $LDIF echo "shadowMin: $MIN" >> $LDIF echo "shadowMax: $MAX" >> $LDIF echo "shadowLastChange: $LAST" >> $LDIF echo >> $LDIF done root@master:~# sh ldapuser.sh root@master:~# ldapadd -x -D cn=admin,dc=server,dc=world -W -f ldapuser.ldif Enter LDAP Password: # admin password adding new entry "uid=squeeze,ou=people,dc=server,dc=world" adding new entry "uid=debian,ou=people,dc=server,dc=world" adding new entry "uid=ubuntu,ou=people,dc=server,dc=world" adding new entry "uid=fedora,ou=people,dc=server,dc=world" adding new entry "uid=suse,ou=people,dc=server,dc=world" adding new entry "uid=cent,ou=people,dc=server,dc=world" |
| [5] | Add existing local groups to LDAP directory |
|
root@master:~# vi ldapgroup.sh # extract local groups who have 4-digit UID # an example
#!/bin/bash SUFFIX='dc=server,dc=world' LDIF='ldapgroup.ldif' echo -n > $LDIF for line in `grep "x:[1-9][0-9][0-9][0-9]:" /etc/group` do CN=`echo $line | cut -d: -f1` GID=`echo $line | cut -d: -f3` echo "dn: cn=$CN,ou=groups,$SUFFIX" >> $LDIF echo "objectClass: posixGroup" >> $LDIF echo "cn: $CN" >> $LDIF echo "gidNumber: $GID" >> $LDIF users=`echo $line | cut -d: -f4 | sed "s/,/ /g"` for user in ${users} ; do echo "memberUid: ${user}" >> $LDIF done echo >> $LDIF done root@master:~# sh ldapgroup.sh root@master:~# ldapadd -x -D cn=admin,dc=server,dc=world -W -f ldapgroup.ldif Enter LDAP Password: # admin password adding new entry "cn=squeeze,ou=groups,dc=server,dc=world" adding new entry "cn=debian,ou=groups,dc=server,dc=world" adding new entry "cn=ubuntu,ou=groups,dc=server,dc=world" adding new entry "cn=fedora,ou=groups,dc=server,dc=world" adding new entry "cn=suse,ou=groups,dc=server,dc=world" adding new entry "cn=cent,ou=groups,dc=server,dc=world" |
| [6] | If you'd like to delete User or Group in LDAP, Do as below. |
|
root@master:~# ldapdelete -x -W -D 'cn=admin,dc=server,dc=world' "uid=debian,ou=people,dc=server,dc=world" Enter LDAP Password: root@master:~# ldapdelete -x -W -D 'cn=admin,dc=server,dc=world' "cn=debian,ou=groups,dc=server,dc=world" Enter LDAP Password: |
Matched Content