Apache2 : Configure mod_security2024/05/31 |
|
Enable [mod_security] module to configure Web Application Firewall (WAF). |
|
| [1] | Install [mod_security]. |
|
root@www:~# apt -y install libapache2-mod-security2
|
| [2] | Enable [mod_security]. |
|
root@www:~# cp -p /etc/modsecurity/modsecurity.conf-recommended /etc/modsecurity/modsecurity.conf
root@www:~#
vi /etc/modsecurity/modsecurity.conf
line 7 : [SecRuleEngine DetectionOnly] is set as default, it does not block actions
# if you'd like to block actions, change to [SecRuleEngine On]
SecRuleEngine DetectionOnly
.....
.....
|
| [3] |
It's possible to write a rule like follows. ⇒ SecRule VARIABLES OPERATOR [ACTIONS]
Each parameter has many kind of values, refer to official documents below. |
| [4] | For Example, set some rules and verify it works normally. |
|
root@www:~#
vi /etc/modsecurity/localrules.conf # default action when matching rules SecDefaultAction "phase:2,deny,log,status:406" # [etc/passwd] is included in request URI SecRule REQUEST_URI "etc/passwd" "id:'500001'" # [../] is included in request URI SecRule REQUEST_URI "\.\./" "id:'500002'" # [<SCRIPT] is included in arguments SecRule ARGS "<[Ss][Cc][Rr][Ii][Pp][Tt]" "id:'500003'" # [SELECT FROM] is included in arguments SecRule ARGS "[Ss][Ee][Ll][Ee][Cc][Tt][[:space:]]+[Ff][Rr][Oo][Mm]" "id:'500004'" systemctl reload apache2
|
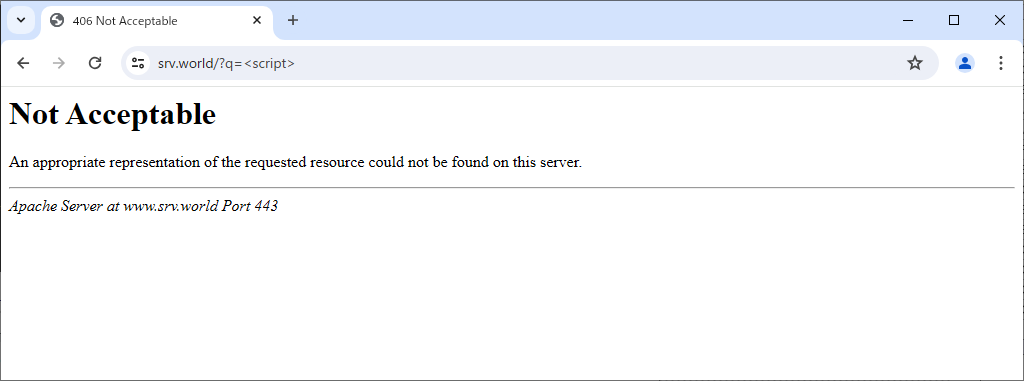
| [5] | Access to the URI which includes words you set and verify it works normally. |
|
| [6] | The logs for [mod_security] is placed in the directory like follows. |
|
root@www:~# cat /var/log/apache2/modsec_audit.log --a63a834d-H-- Message: Access denied with code 406 (phase 2). Pattern match "<[Ss][Cc][Rr][Ii][Pp][Tt]" at ARGS:q. [file "/etc/modsecurity/localrules.conf"] [line "7"] [id "500003"] Apache-Error: [file "apache2_util.c"] [line 275] [level 3] [client 10.0.0.5] ModSecurity: Access denied with code 406 (phase 2). Pattern match "<[Ss][Cc][Rr][Ii][Pp][Tt]" at ARGS:q. [file "/etc/modsecurity/localrules.conf"] [line "7"] [id "500003"] [hostname "www.srv.world"] [uri "/"] [unique_id "ZlkdZvgCcK1SfGOlNumoPQAAAEQ"] Action: Intercepted (phase 2) Stopwatch: 1717116262897063 1200 (- - -) Stopwatch2: 1717116262897063 1200; combined=523, p1=438, p2=6, p3=0, p4=0, p5=79, sr=33, sw=0, l=0, gc=0 Response-Body-Transformed: Dechunked Producer: ModSecurity for Apache/2.9.7 (http://www.modsecurity.org/); OWASP_CRS/3.3.5. Server: Apache Engine-Mode: "ENABLED" ..... ..... |
| [7] | General rules are provided and applied by default under the directory below. However maybe you need to customize them for your own web sites not to block necessary requests. |
|
root@www:~# ll /usr/share/modsecurity-crs/rules total 696 drwxr-xr-x 2 root root 4096 May 31 00:41 ./ drwxr-xr-x 4 root root 4096 May 31 00:41 ../ -rw-r--r-- 1 root root 13901 Oct 1 2023 REQUEST-901-INITIALIZATION.conf -rw-r--r-- 1 root root 13625 Oct 1 2023 REQUEST-903.9001-DRUPAL-EXCLUSION-RULES.conf -rw-r--r-- 1 root root 25882 Oct 1 2023 REQUEST-903.9002-WORDPRESS-EXCLUSION-RULES.conf -rw-r--r-- 1 root root 10712 Oct 1 2023 REQUEST-903.9003-NEXTCLOUD-EXCLUSION-RULES.conf -rw-r--r-- 1 root root 7892 Oct 1 2023 REQUEST-903.9004-DOKUWIKI-EXCLUSION-RULES.conf -rw-r--r-- 1 root root 1946 Oct 1 2023 REQUEST-903.9005-CPANEL-EXCLUSION-RULES.conf -rw-r--r-- 1 root root 18406 Oct 1 2023 REQUEST-903.9006-XENFORO-EXCLUSION-RULES.conf -rw-r--r-- 1 root root 1625 Oct 1 2023 REQUEST-905-COMMON-EXCEPTIONS.conf -rw-r--r-- 1 root root 10402 Oct 1 2023 REQUEST-910-IP-REPUTATION.conf -rw-r--r-- 1 root root 2684 Oct 1 2023 REQUEST-911-METHOD-ENFORCEMENT.conf -rw-r--r-- 1 root root 10668 Oct 1 2023 REQUEST-912-DOS-PROTECTION.conf -rw-r--r-- 1 root root 7139 Oct 1 2023 REQUEST-913-SCANNER-DETECTION.conf -rw-r--r-- 1 root root 54347 Oct 1 2023 REQUEST-920-PROTOCOL-ENFORCEMENT.conf -rw-r--r-- 1 root root 16808 Oct 1 2023 REQUEST-921-PROTOCOL-ATTACK.conf -rw-r--r-- 1 root root 4482 Oct 1 2023 REQUEST-922-MULTIPART-ATTACK.conf -rw-r--r-- 1 root root 6028 Oct 1 2023 REQUEST-930-APPLICATION-ATTACK-LFI.conf -rw-r--r-- 1 root root 5752 Oct 1 2023 REQUEST-931-APPLICATION-ATTACK-RFI.conf -rw-r--r-- 1 root root 54880 Oct 1 2023 REQUEST-932-APPLICATION-ATTACK-RCE.conf ..... ..... |
Matched Content