Apache httpd : Configure mod_security2022/03/16 |
|
Enable [mod_security] module to configure Web Application Firewall (WAF).
|
|
| [1] | Install [mod_security]. |
|
[root@www ~]# dnf -y install mod_security
|
| [2] | After installing, configuration files are placed under the directory like follows and the setting is enabled. Some settings are already set in it and also you can add your own rules. |
|
[root@www ~]# cat /etc/httpd/conf.d/mod_security.conf
<IfModule mod_security2.c>
# Default recommended configuration
SecRuleEngine On
SecRequestBodyAccess On
SecRule REQUEST_HEADERS:Content-Type "text/xml" \
"id:'200000',phase:1,t:none,t:lowercase,pass,nolog,ctl:requestBodyProcessor=XML"
SecRequestBodyLimit 13107200
SecRequestBodyNoFilesLimit 131072
SecRequestBodyInMemoryLimit 131072
SecRequestBodyLimitAction Reject
SecRule REQBODY_ERROR "!@eq 0" \
.....
.....
# if you would not like to block requests if matchs rules,
# specify change to the parameter [SecRuleEngine DetectionOnly]
|
| [3] |
It's possible to write a rule like follows.
⇒ SecRule VARIABLES OPERATOR [ACTIONS]
Each parameter has many kind of values, refer to official documents below.
https://github.com/SpiderLabs/ModSecurity/wiki |
| [4] | For Example, set some rules and verify it works normally. |
|
[root@www ~]#
vi /etc/httpd/modsecurity.d/local_rules/modsecurity_localrules.conf # default action when matching rules SecDefaultAction "phase:2,deny,log,status:406" # [etc/passwd] is included in request URI SecRule REQUEST_URI "etc/passwd" "id:'500001'" # [../] is included in request URI SecRule REQUEST_URI "\.\./" "id:'500002'" # [<SCRIPT] is included in arguments SecRule ARGS "<[Ss][Cc][Rr][Ii][Pp][Tt]" "id:'500003'" # [SELECT FROM] is included in arguments SecRule ARGS "[Ss][Ee][Ll][Ee][Cc][Tt][[:space:]]+[Ff][Rr][Oo][Mm]" "id:'500004'" systemctl restart httpd
|
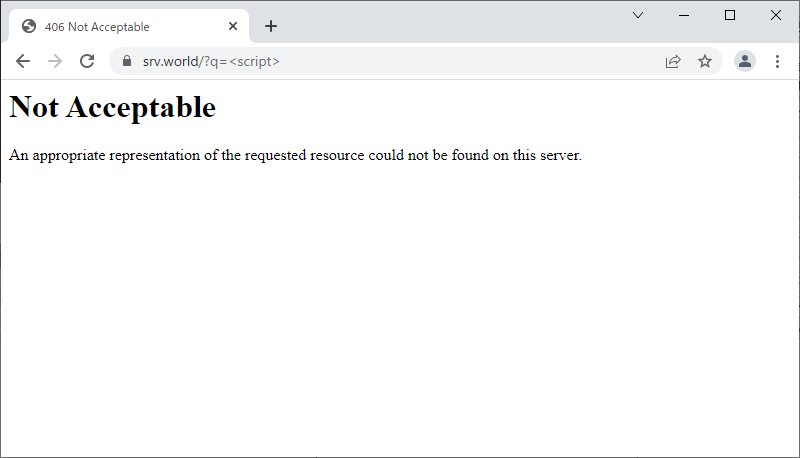
| [5] | Access to the URI which includes words you set and verify it works normally. |
|
| [6] | The logs for [mod_security] is placed in the directory like follows. |
|
[root@www ~]# cat /var/log/httpd/modsec_audit.log ..... ..... --07b1e407-F-- HTTP/1.1 406 Not Acceptable Content-Length: 249 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=iso-8859-1 --07b1e407-E-- --07b1e407-H-- Message: Access denied with code 406 (phase 2). Pattern match "<[Ss][Cc][Rr][Ii][Pp][Tt]" at ARGS:q. [file "/etc/httpd/modsecurity.d/local_rules/modsecurity_localrules.conf"] [line "15"] [id "500003"] Apache-Error: [file "apache2_util.c"] [line 271] [level 3] [client 10.0.0.5] ModSecurity: Access denied with code 406 (phase 2). Pattern match "<[Ss][Cc][Rr][Ii][Pp][Tt]" at ARGS:q. [file "/etc/httpd/modsecurity.d/local_rules/modsecurity_localrules.conf"] [line "15"] [id "500003"] [hostname "www.srv.world"] [uri "/"] [unique_id "YjFJOpn4G-IerYngYR53lQAAAFU"] Action: Intercepted (phase 2) Stopwatch: 1647397178888826 797 (- - -) Stopwatch2: 1647397178888826 797; combined=52, p1=18, p2=32, p3=0, p4=0, p5=2, sr=0, sw=0, l=0, gc=0 Response-Body-Transformed: Dechunked Producer: ModSecurity for Apache/2.9.3 (http://www.modsecurity.org/). Server: Apache Engine-Mode: "ENABLED" --07b1e407-Z-- |
| [7] | General rules are provided from official repository and it's easy to apply them like follows. But maybe you need to customize them for your own web sites not to block necessary requests. |
|
[root@www ~]#
dnf -y install mod_security_crs # rules are placed like follows # they are linked into the directory [/etc/httpd/modsecurity.d/activated_rules] [root@www ~]# ll /usr/share/mod_modsecurity_crs/rules total 668 -rw-r--r--. 1 root root 786 Aug 10 2021 crawlers-user-agents.data -rw-r--r--. 1 root root 551 Aug 10 2021 iis-errors.data -rw-r--r--. 1 root root 933 Aug 10 2021 java-classes.data -rw-r--r--. 1 root root 264 Aug 10 2021 java-code-leakages.data -rw-r--r--. 1 root root 240 Aug 10 2021 java-errors.data -rw-r--r--. 1 root root 31209 Aug 10 2021 lfi-os-files.data -rw-r--r--. 1 root root 5409 Aug 10 2021 php-config-directives.data -rw-r--r--. 1 root root 9201 Aug 10 2021 php-errors.data -rw-r--r--. 1 root root 683 Aug 10 2021 php-function-names-933150.data -rw-r--r--. 1 root root 21282 Aug 10 2021 php-function-names-933151.data -rw-r--r--. 1 root root 224 Aug 10 2021 php-variables.data -rw-r--r--. 1 root root 13513 Aug 10 2021 REQUEST-901-INITIALIZATION.conf -rw-r--r--. 1 root root 13069 Aug 10 2021 REQUEST-903.9001-DRUPAL-EXCLUSION-RULES.conf -rw-r--r--. 1 root root 25812 Aug 10 2021 REQUEST-903.9002-WORDPRESS-EXCLUSION-RULES.conf -rw-r--r--. 1 root root 10642 Aug 10 2021 REQUEST-903.9003-NEXTCLOUD-EXCLUSION-RULES.conf -rw-r--r--. 1 root root 7822 Aug 10 2021 REQUEST-903.9004-DOKUWIKI-EXCLUSION-RULES.conf -rw-r--r--. 1 root root 1876 Aug 10 2021 REQUEST-903.9005-CPANEL-EXCLUSION-RULES.conf -rw-r--r--. 1 root root 18336 Aug 10 2021 REQUEST-903.9006-XENFORO-EXCLUSION-RULES.conf -rw-r--r--. 1 root root 1555 Aug 10 2021 REQUEST-905-COMMON-EXCEPTIONS.conf -rw-r--r--. 1 root root 10448 Aug 10 2021 REQUEST-910-IP-REPUTATION.conf -rw-r--r--. 1 root root 2614 Aug 10 2021 REQUEST-911-METHOD-ENFORCEMENT.conf -rw-r--r--. 1 root root 10743 Aug 10 2021 REQUEST-912-DOS-PROTECTION.conf -rw-r--r--. 1 root root 7069 Aug 10 2021 REQUEST-913-SCANNER-DETECTION.conf -rw-r--r--. 1 root root 50184 Aug 10 2021 REQUEST-920-PROTOCOL-ENFORCEMENT.conf -rw-r--r--. 1 root root 13208 Aug 10 2021 REQUEST-921-PROTOCOL-ATTACK.conf -rw-r--r--. 1 root root 5958 Aug 10 2021 REQUEST-930-APPLICATION-ATTACK-LFI.conf -rw-r--r--. 1 root root 5678 Aug 10 2021 REQUEST-931-APPLICATION-ATTACK-RFI.conf -rw-r--r--. 1 root root 54798 Aug 10 2021 REQUEST-932-APPLICATION-ATTACK-RCE.conf -rw-r--r--. 1 root root 32617 Aug 10 2021 REQUEST-933-APPLICATION-ATTACK-PHP.conf -rw-r--r--. 1 root root 3927 Aug 10 2021 REQUEST-934-APPLICATION-ATTACK-NODEJS.conf -rw-r--r--. 1 root root 40398 Aug 10 2021 REQUEST-941-APPLICATION-ATTACK-XSS.conf -rw-r--r--. 1 root root 70457 Aug 10 2021 REQUEST-942-APPLICATION-ATTACK-SQLI.conf -rw-r--r--. 1 root root 5204 Aug 10 2021 REQUEST-943-APPLICATION-ATTACK-SESSION-FIXATION.conf -rw-r--r--. 1 root root 15288 Aug 10 2021 REQUEST-944-APPLICATION-ATTACK-JAVA.conf -rw-r--r--. 1 root root 4094 Aug 10 2021 REQUEST-949-BLOCKING-EVALUATION.conf -rw-r--r--. 1 root root 4714 Aug 10 2021 RESPONSE-950-DATA-LEAKAGES.conf -rw-r--r--. 1 root root 17863 Aug 10 2021 RESPONSE-951-DATA-LEAKAGES-SQL.conf -rw-r--r--. 1 root root 3515 Aug 10 2021 RESPONSE-952-DATA-LEAKAGES-JAVA.conf -rw-r--r--. 1 root root 4951 Aug 10 2021 RESPONSE-953-DATA-LEAKAGES-PHP.conf -rw-r--r--. 1 root root 5764 Aug 10 2021 RESPONSE-954-DATA-LEAKAGES-IIS.conf -rw-r--r--. 1 root root 4207 Aug 10 2021 RESPONSE-959-BLOCKING-EVALUATION.conf -rw-r--r--. 1 root root 6801 Aug 10 2021 RESPONSE-980-CORRELATION.conf -rw-r--r--. 1 root root 2043 Aug 10 2021 restricted-files.data -rw-r--r--. 1 root root 390 Aug 10 2021 restricted-upload.data -rw-r--r--. 1 root root 216 Aug 10 2021 scanners-headers.data -rw-r--r--. 1 root root 418 Aug 10 2021 scanners-urls.data -rw-r--r--. 1 root root 4869 Aug 10 2021 scanners-user-agents.data -rw-r--r--. 1 root root 717 Aug 10 2021 scripting-user-agents.data -rw-r--r--. 1 root root 1894 Aug 10 2021 sql-errors.data -rw-r--r--. 1 root root 1380 Aug 10 2021 unix-shell.data -rw-r--r--. 1 root root 3920 Aug 10 2021 windows-powershell-commands.data |
Matched Content