FreeIPA : FreeIPA trust AD2022/03/23 |
|
Configure Cross Forest Trust between FreeIPA domain and Windows Active Directory domain.
This example is based on the environment like follows.
+----------------------+ | +----------------------+ | [ FreeIPA (CentOS) ] |10.0.0.40 | 10.0.0.100| [ AD (Win 2022) ] | | dlp.ipa.srv.world +----------+-----------+ fd3s.ad.srv.world | | | | | +----------------------+ +----------------------+ |
| [1] | Install required packages and Setup trust on FreeIPA Server. |
|
[root@dlp ~]#
[root@dlp ~]# dnf -y install ipa-server-trust-ad ipa-adtrust-install The log file for this installation can be found in /var/log/ipaserver-adtrust-install.log ============================================================================== This program will setup components needed to establish trust to AD domains for the IPA Server. This includes: * Configure Samba * Add trust related objects to IPA LDAP server To accept the default shown in brackets, press the Enter key. Configuring cross-realm trusts for IPA server requires password for user 'admin'. This user is a regular system account used for IPA server administration. # FreeIPA admin password admin password: WARNING: The smb.conf already exists. Running ipa-adtrust-install will break your existing samba configuration. # confirm smb.conf is over written Do you wish to continue? [no]: yes Do you want to enable support for trusted domains in Schema Compatibility plugin? This will allow clients older than SSSD 1.9 and non-Linux clients to work with trusted users. # enable slapi-nis or not Enable trusted domains support in slapi-nis? [no]: The following operations may take some minutes to complete. Please wait until the prompt is returned. Configuring CIFS [1/23]: validate server hostname [2/23]: stopping smbd [3/23]: creating samba domain object ..... ..... ============================================================================= Setup complete You must make sure these network ports are open: TCP Ports: * 135: epmap * 138: netbios-dgm * 139: netbios-ssn * 445: microsoft-ds * 1024..1300: epmap listener range * 3268: msft-gc UDP Ports: * 138: netbios-dgm * 139: netbios-ssn * 389: (C)LDAP * 445: microsoft-ds See the ipa-adtrust-install(1) man page for more details ============================================================================= # if firewalld is running, allow service [root@dlp ~]# firewall-cmd --add-service=freeipa-trust success [root@dlp ~]# firewall-cmd --runtime-to-permanent success |
| [2] | Add DNS Setting on FreeIPA Server. |
|
# ipa dnsforwardzone-add [AD domain name] --forwarder=[AD IP address] --forward-policy=only [root@dlp ~]# ipa dnsforwardzone-add ad.srv.world --forwarder=10.0.0.100 --forward-policy=only Server will check DNS forwarder(s). This may take some time, please wait ... Zone name: ad.srv.world. Active zone: TRUE Zone forwarders: 10.0.0.100 Forward policy: only # ipa dnszone-mod [IPA domain name] --allow-transfer=[AD IP address] [root@dlp ~]# ipa dnszone-mod ipa.srv.world --allow-transfer=10.0.0.100 Zone name: ipa.srv.world. Active zone: TRUE Authoritative nameserver: dlp.ipa.srv.world. Administrator e-mail address: hostmaster.ipa.srv.world. SOA serial: 1648005848 SOA refresh: 3600 SOA retry: 900 SOA expire: 1209600 SOA minimum: 3600 BIND update policy: grant IPA.SRV.WORLD krb5-self * A; grant IPA.SRV.WORLD krb5-self * AAAA; grant IPA.SRV.WORLD krb5-self * SSHFP; Dynamic update: TRUE Allow query: any; Allow transfer: 10.0.0.100; |
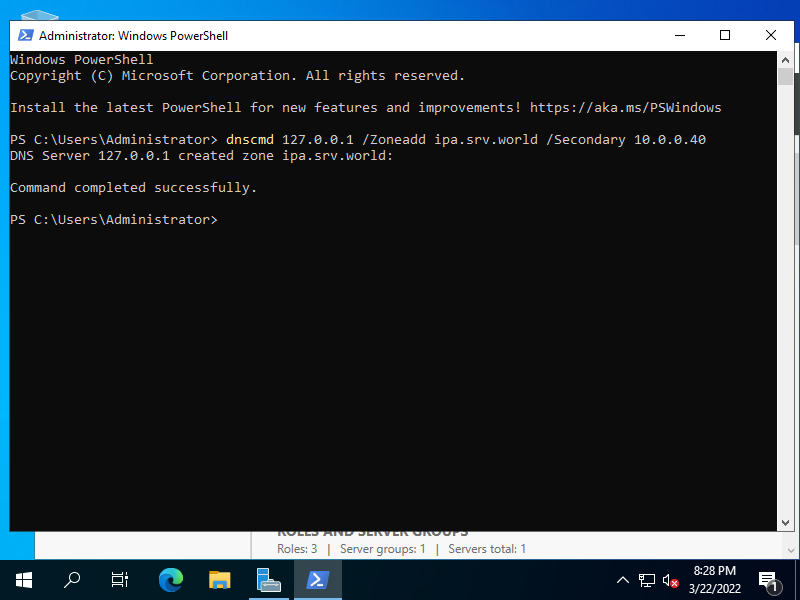
| [3] | Add FreeIPA Domain to Zones on Windows Active Directory Server. ⇒ dnscmd 127.0.0.1 /ZoneAdd [FreeIPA domain name] /Secondary [FreeIPA IP address] |
|
| [4] | Verify Name resolution and if no problem, Setup trust. |
|
[root@dlp ~]# dig SRV _ldap._tcp.ipa.srv.world ; <<>> DiG 9.16.23-RH <<>> SRV _ldap._tcp.ipa.srv.world ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 913 ;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 3 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 1232 ; COOKIE: 054a55dba44a8b5601000000623a9457340f92b86268b581 (good) ;; QUESTION SECTION: ;_ldap._tcp.ipa.srv.world. IN SRV ;; ANSWER SECTION: _ldap._tcp.ipa.srv.world. 86400 IN SRV 0 100 389 dlp.ipa.srv.world. _ldap._tcp.ipa.srv.world. 86400 IN SRV 0 100 389 node01.ipa.srv.world. ;; ADDITIONAL SECTION: dlp.ipa.srv.world. 1200 IN A 10.0.0.40 node01.ipa.srv.world. 1200 IN A 10.0.0.61 ;; Query time: 0 msec ;; SERVER: 127.0.0.1#53(127.0.0.1) ;; WHEN: Wed Mar 23 12:30:31 JST 2022 ;; MSG SIZE rcvd: 190[root@dlp ~]# dig SRV _ldap._tcp.ad.srv.world ; <<>> DiG 9.16.23-RH <<>> SRV _ldap._tcp.ad.srv.world ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 9864 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 1232 ; COOKIE: 7ac8a9d0c54230ee01000000623a94846202d8eb1778ec4d (good) ;; QUESTION SECTION: ;_ldap._tcp.ad.srv.world. IN SRV ;; ANSWER SECTION: _ldap._tcp.ad.srv.world. 600 IN SRV 0 100 389 fd3s.ad.srv.world. ;; Query time: 798 msec ;; SERVER: 127.0.0.1#53(127.0.0.1) ;; WHEN: Wed Mar 23 12:31:16 JST 2022 ;; MSG SIZE rcvd: 117 # ipa trust-add --type=ad [AD domain name] --admin Administrator --password [root@dlp ~]# ipa trust-add --two-way=true --type=ad ad.srv.world --admin Administrator --password Active Directory domain administrator's password: ----------------------------------------------------- Added Active Directory trust for realm "ad.srv.world" ----------------------------------------------------- Realm name: ad.srv.world Domain NetBIOS name: FD3S01 Domain Security Identifier: S-1-5-21-726412840-3773945212-2352305327 Trust direction: Two-way trust Trust type: Active Directory domain Trust status: Established and verified # verify possible to get any AD user info [root@dlp ~]# id Serverworld@ad.srv.world uid=1596401103(serverworld@ad.srv.world) gid=1596401103(serverworld@ad.srv.world) groups=1596401103(serverworld@ad.srv.world),1596400513(domain users@ad.srv.world) # set if you need (create home directory at initial login) [root@dlp ~]# authselect enable-feature with-mkhomedir [root@dlp ~]# systemctl enable --now oddjobd
# verify possible to login with any AD user [root@dlp ~]# exit logout CentOS Stream 9 Kernel 5.14.0-71.el9.x86_64 on an x86_64 Activate the web console with: systemctl enable --now cockpit.socket dlp login: Serverworld@ad.srv.world Password: [serverworld@ad.srv.world@dlp ~]$ id uid=1596401103(serverworld@ad.srv.world) gid=1596401103(serverworld@ad.srv.world) groups=1596401103(serverworld@ad.srv.world),1596400513(domain users@ad.srv.world) context=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 # just logined |
Matched Content